Welcome to Defense in DepthGeoff Belknap
Lydbøger indlæst af David Spark
- Security MetricsGeoff Belknap
- PrivacyGeoff Belknap
- Building an Information Security CouncilGeoff Belknap
- Insider ThreatsGeoff Belknap
- Secure Controls FrameworkGeoff Belknap
- Threat IntelligenceGeoff Belknap
- Security IS the BusinessGeoff Belknap
- RSA 2019: Success or Failure?Geoff Belknap
- CISO BurnoutGeoff Belknap
- Tools for Managing 3rd Party RiskGeoff Belknap
- Software Fixing Hardware ProblemsGeoff Belknap
- Machine Learning FailuresGeoff Belknap
- Privileged Access ManagementGeoff Belknap
- Vulnerability ManagementGeoff Belknap
- Is the Cybersecurity Industry Solving Our Problems?Geoff Belknap
- How CISOs Discover New SolutionsGeoff Belknap
- Cybersecurity HiringGeoff Belknap
- Managing Obsolete (Yet Business Critical) SystemsGeoff Belknap
- ERP SecurityGeoff Belknap
- Amplifying Your Security PostureGeoff Belknap
- Camry SecurityGeoff Belknap
- Tool ConsolidationGeoff Belknap
- Economics of DataGeoff Belknap
- CISO Series One Year ReviewGeoff Belknap
- Cyber HarassmentGeoff Belknap
- Bad Best PracticesGeoff Belknap
- Hacker CultureGeoff Belknap
- ATT&CK MatrixGeoff Belknap
- Proactive SecurityGeoff Belknap
- 100% SecurityGeoff Belknap
- Employee HackingGeoff Belknap
- Cybersecurity ExcusesGeoff Belknap
- Top CISO Communication IssuesGeoff Belknap
- RansomwareGeoff Belknap
- ResiliencyGeoff Belknap
- Securing the New InternetGeoff Belknap
- User-Centric SecurityGeoff Belknap
- Cyber Defense MatrixGeoff Belknap
- Best Starting Security FrameworkGeoff Belknap
- Is Product Security Improving?Geoff Belknap
- The Cloud and Shared SecurityGeoff Belknap
- Cybersecurity and the MediaGeoff Belknap
- Cybersecurity Readiness as Hiring CriteriaGeoff Belknap
- InfoSec Trends for 2020Geoff Belknap
- UX in CybersecurityGeoff Belknap
- Account TakeoverGeoff Belknap
- Building a Fully Remote Security TeamGeoff Belknap
- The Iran Cybersecurity ThreatGeoff Belknap
- Presenting to the BoardGeoff Belknap
- Post Breach Desperation and Salary NegotiationsGeoff Belknap
- When Are CISOs Responsible for Breaches?Geoff Belknap
- Lack of Diversity in CybersecurityGeoff Belknap
- Personality Tests in the WorkplaceGeoff Belknap
- Toxic Security TeamsGeoff Belknap
- CISO TenureGeoff Belknap
- Hybrid CloudGeoff Belknap
- Who Should the CISO Report To?Geoff Belknap
- Is Governance the Most Important Part of GRC?Geoff Belknap
- Internet of ThingsGeoff Belknap
- Responsible DisclosureGeoff Belknap
- Should Risk Lead GRC?Geoff Belknap
- Fix Security Problems with What You've GotGeoff Belknap
- DevSecOpsGeoff Belknap
- Asset ValuationGeoff Belknap
- Prevention vs. Detection and ContainmentGeoff Belknap
- Data ClassificationGeoff Belknap
- Bug BountiesGeoff Belknap
- Shared AccountsGeoff Belknap
- Role of the BISOGeoff Belknap
- Security BudgetsGeoff Belknap
- Drudgery of CybercrimeGeoff Belknap
- Shared Threat IntelligenceGeoff Belknap
- API SecurityGeoff Belknap
- Securing a Cloud MigrationGeoff Belknap
- InfoSec FatigueGeoff Belknap
- Secure AccessGeoff Belknap
- How Vendors Should Approach CISOsGeoff Belknap
- Trusting Security Vendor ClaimsGeoff Belknap
- Junior Cyber PeopleGeoff Belknap
- What Cyber Pro Are You Trying to Hire?Geoff Belknap
- When Red Teams Break DownGeoff Belknap
- Is College Necessary for a Job in Cybersecurity?Geoff Belknap
- Calling Users StupidGeoff Belknap
- XDR: Extended Detection and ResponseGeoff Belknap
- Legal Protection for CISOsGeoff Belknap
- Privacy Is An Uphill BattleGeoff Belknap
- Measuring the Success of Your Security ProgramGeoff Belknap
- Leaked Secrets in Code RepositoriesGeoff Belknap
- Securing Digital TransformationsGeoff Belknap
- What's an Entry Level Cybersecurity Job?Geoff Belknap
- Data Protection and VisibilityGeoff Belknap
- Why Don't More Companies Take Cybersecurity Seriously?Geoff Belknap
- Imposter SyndromeGeoff Belknap
- Inherently Vulnerable By DesignGeoff Belknap
- Should CISOs Be Licensed Professionals?Geoff Belknap
- Are our Data Protection Strategies Evolving?Geoff Belknap
- Building a Security TeamGeoff Belknap
- How Do You Know if You're Good at Security?Geoff Belknap
- Does a CISO Need Tech Skills?Geoff Belknap
- How to Make Cybersecurity More EfficientGeoff Belknap
- Data DestructionGeoff Belknap
- Should Finance or Legal Mentor Cyber?Geoff Belknap
- How Much Log Data Is Enough?Geoff Belknap
- Vendor CISOsGeoff Belknap
- What Is Security's Mission?Geoff Belknap
- Cloud Security MythsGeoff Belknap
- Cybersecurity Isn’t That DifficultGeoff Belknap
- Securing the Super Bowl and Other Huge EventsGeoff Belknap
- MentoringGeoff Belknap
- What’s the Obsession with Zero Trust?Geoff Belknap
- Insider RiskGeoff Belknap
- Do Startups Need a CISO?Geoff Belknap
- How Much Do You Know About Your Data?Geoff Belknap
- Security Hygiene for Software DevelopmentGeoff Belknap
- Hiring Talent with No Security ExperienceGeoff Belknap
- Fear of AutomationGeoff Belknap
- Starting Pay for Cyber StaffGeoff Belknap
- Cloud Configuration FailsGeoff Belknap
- Salesforce SecurityGeoff Belknap
- Retaining Cyber TalentGeoff Belknap
- CISO Recruiting Is BrokenGeoff Belknap
- Educating the Board About CybersecurityGeoff Belknap
- How do I get my first cybersecurity job?Geoff Belknap
- Measuring the Success of Cloud SecurityGeoff Belknap
- What's the Value of Certifications?Geoff Belknap
- How Does Ransomware Enter the Network?Geoff Belknap
- First Steps as a CISOGeoff Belknap
- Managing Lateral MovementGeoff Belknap
- Preventing RansomwareGeoff Belknap
- Cybersecurity Is Not Easy to Get IntoGeoff Belknap
- Convergence of SIEM and SOARGeoff Belknap
- Can Technology Solve Phishing?Geoff Belknap
- Ransomware Kill ChainGeoff Belknap
- The "Are We Secure?" QuestionGeoff Belknap
- How to Be a Vendor that CISOs LoveGeoff Belknap
- Why Is Security Recruiting So Broken?Geoff Belknap
- Proactive Vulnerability ManagementGeoff Belknap
- Ageism in CybersecurityGeoff Belknap
- How Do We Turn Tables Against Adversaries?Geoff Belknap
- How Do You Measure Cybersecurity Success?Geoff Belknap
- Convergence of Physical and Digital SecurityGeoff Belknap
- How Can We Simplify Security?Geoff Belknap
- When Social Engineering Bypasses Our Cyber ToolsGeoff Belknap
- Promises of AutomationGeoff Belknap
- Making Cybersecurity Faster and More ResponsiveGeoff Belknap
- DDoS SolutionsGeoff Belknap
- What Should We Stop Doing in Cybersecurity?Geoff Belknap
- Is Your Data Safer in the Cloud?Geoff Belknap
- How to Pitch to a Security AnalystGeoff Belknap
- Building a Cybersecurity CultureGeoff Belknap
- When Vendors Pounce on New CISOsGeoff Belknap
- Offensive SecurityGeoff Belknap
- Building a Data-First Security ProgramGeoff Belknap
- How to Think Like a CybercrookGeoff Belknap
- Start a Cybersecurity Department from ScratchGeoff Belknap
- Virtual PatchingGeoff Belknap
- Training for a Cyber DisasterGeoff Belknap
- Why Do So Many Cybersecurity Products Suck?Geoff Belknap
- Technical vs. Compliance ProfessionalsGeoff Belknap
- Is Shift Left Working?Geoff Belknap
- Are We Taking Zero Trust Too Far?Geoff Belknap
- Does the Cybersecurity Industry Suck?Geoff Belknap
- Who Investigates Cyber Solutions?Geoff Belknap
- Where's the Trust in Zero Trust?Geoff Belknap
- Onboarding Cyber Professionals with No ExperienceGeoff Belknap
- Building a Security Awareness Training ProgramGeoff Belknap
- Getting Ahead of the Ongoing Malware FightGeoff Belknap
- Can Security Be a Profit Center?Geoff Belknap
- How Is Our Data Being Weaponized Against Us?Geoff Belknap
- How Can We Improve Recruiting of CISOs and Security Leaders?Geoff Belknap
- How Can You Tell If Your Security Program Is Improving?Geoff Belknap
- What Is Attack Surface Profiling?Geoff Belknap
- Data Protection for Whatever Comes NextGeoff Belknap
- Practical Cybersecurity for IT ProfessionalsGeoff Belknap
- We're All Still Learning CyberGeoff Belknap
- Minimizing Damage from a BreachGeoff Belknap
- Roles to Prepare You to Be a CISOGeoff Belknap
- How to Follow Up With a CISOGeoff Belknap
- Can You Have Culture Fit and Diversity, or Are They Mutually Exclusive?Geoff Belknap
- Managing the Onslaught of FilesGeoff Belknap
- How to Build a Greenfield Security ProgramGeoff Belknap
- Cybersecurity BurnoutGeoff Belknap
- How to Engage with Non-Technical Business LeadersGeoff Belknap
- Moving Security from a Prevention to a Resilience StrategyGeoff Belknap
- Walk a Mile in a Security Recruiter's ShoesGeoff Belknap
- How Can We Make Sense of Cybersecurity Titles?Geoff Belknap
- Cybersecurity BudgetsGeoff Belknap
- Do We Need a Marketing Manager for the Security Team?Geoff Belknap
- Reducing the Attack SurfaceGeoff Belknap
- How Should We Gauge a Company's Cyber Health?Geoff Belknap
- Can You Be a vCISO If You’ve Never Been a CISO?Geoff Belknap
- How Should We Discuss Cyber With the C-Suite?Geoff Belknap
- Do CISOs Have More Stress than Other C-Suite JobsGeoff Belknap
- Ambulance Chasing Security VendorsGeoff Belknap
- Securing Unmanaged AssetsGeoff Belknap
- What Can the Cyber Haves Do for the Cyber Have Nots?Geoff Belknap
- Why Is There a Cybersecurity Skills Gap?Geoff Belknap
- Limitations of Security FrameworksGeoff Belknap
- What Leads a Security Program: Risk or Maturity?Geoff Belknap
- How Can We Improve the Cyber Sales Cycle?Geoff Belknap
- Third Party Risk vs. Third Party TrustGeoff Belknap
- Can You Build a Security Program on Open Source?Geoff Belknap
- How to Become a CISOGeoff Belknap
- Why You Should Be Your Company's Next CISOGeoff Belknap
- Security That Accounts for Human FallibilityGeoff Belknap
- What We Love About Working in CybersecurityGeoff Belknap
- Do Breaches Happen Because the Tool Fails, or the Tool Was Poorly Configured?Geoff Belknap
- How to Always Make a Business Case for SecurityGeoff Belknap
- Gartner Created Product CategoriesGeoff Belknap
- How Should Security Vendors Engage With CISOs?Geoff Belknap
- Successful Cloud SecurityGeoff Belknap
- Do RFPs Work?Geoff Belknap
- Reputational Damage from BreachesGeoff Belknap
- How Must Processes Change to Reduce Risk?Geoff Belknap
- How Should We Trust Entry Level Employees?Geoff Belknap
- How to Create a Positive Security CultureGeoff Belknap
- How To Get More People Into CybersecurityGeoff Belknap
- How Should Security Better Engage with Application Owners?Geoff Belknap
- Let's Write Better Cybersecurity Job DescriptionsGeoff Belknap
- Finding Your Security CommunityGeoff Belknap
- How Do We Get Better Control of Cloud Data?Geoff Belknap
- Securing SaaS ApplicationsGeoff Belknap
- Improving Adoption of Least Privileged AccessGeoff Belknap
- Create A Pipeline of Cyber TalentGeoff Belknap
- Security Concerns with ChatGPTGeoff Belknap
- How Do We Influence Secure Behavior?Geoff Belknap
- How Security Leaders Deal with Intense StressGeoff Belknap
- Getting Ahead Of Your Threat Intelligence ProgramGeoff Belknap
- How to Prime Your Data LakeGeoff Belknap
- Cybersecurity Questions Heard Around the Kitchen TableGeoff Belknap
- How to Manage Users' Desires for New TechnologyGeoff Belknap
- Is Remote Work Helping or Hurting Cybersecurity?Geoff Belknap
- The Value of RSA, Black Hat, and Mega Cyber TradeshowsGeoff Belknap
- New SEC Rules for Cyber SecurityGeoff Belknap
- What's Entry Level in Cybersecurity?Geoff Belknap
- People Are the Top Attack Vector (Not the Weakest Link)Geoff Belknap
- Responsibly Embracing Generative AIGeoff Belknap
- Building a Cyber Strategy for Unknown UnknownsGeoff Belknap
- Mitigating Generative AI RisksGeoff Belknap
- Do We Have to Fix ALL the Critical Vulnerabilities?Geoff Belknap
- Warning Signs You're About To Be AttackedGeoff Belknap
- Doing Third Party Risk Management RightGeoff Belknap
- The Do's and Don'ts of Approaching CISOsGeoff Belknap
- Use Red Teaming To Build, Not Validate, Your Security ProgramGeoff Belknap
- CISOs Responsibilities Before and After an M&AGeoff Belknap
- Is "Compliance Doesn't Equal Security" a Pointless Argument?Geoff Belknap
- Why Do Cybersecurity Startups Fail?Geoff Belknap
- Tracking Anomalous Behaviors of Legitimate IdentitiesGeoff Belknap
- When Is Data an Asset and When Is It a Liability?Geoff Belknap
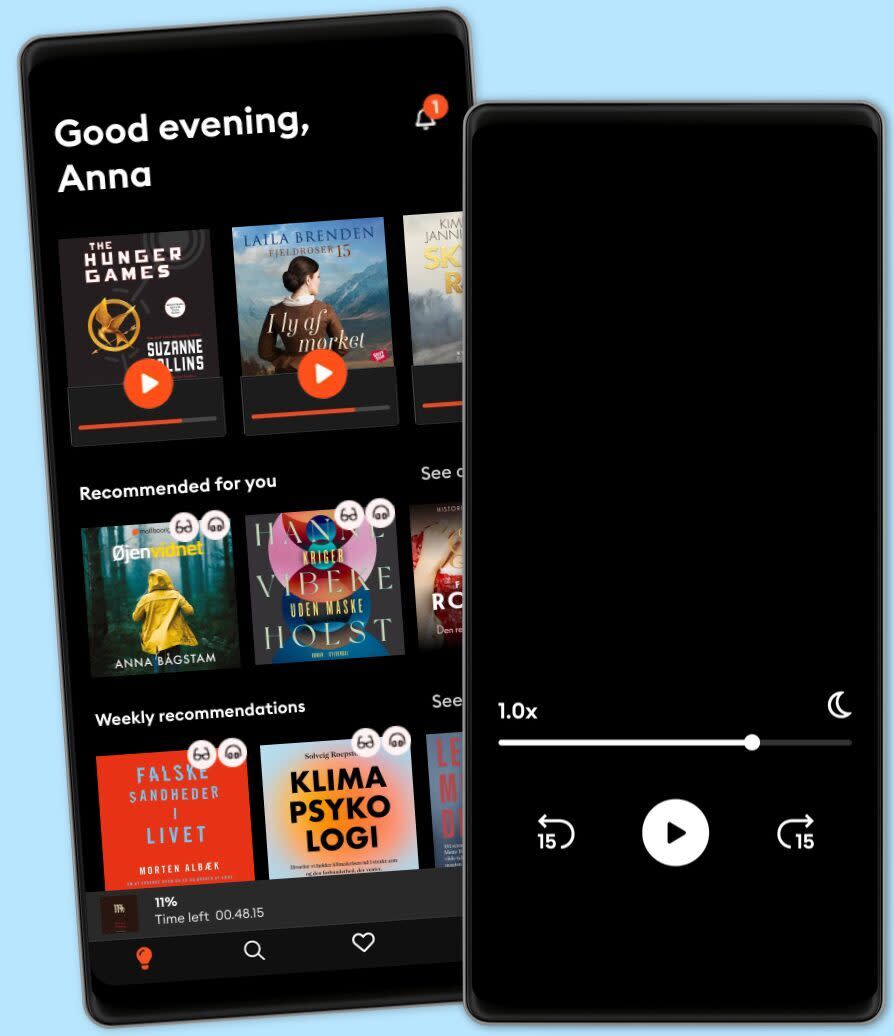
Lyt når som helst, hvor som helst
Nyd den ubegrænsede adgang til tusindvis af spændende e- og lydbøger - helt gratis
- Lyt og læs så meget du har lyst til
- Opdag et kæmpe bibliotek fyldt med fortællinger
- Eksklusive titler + Mofibo Originals
- Opsig når som helst
Brugbare links
Sprog og region
Dansk
Danmark