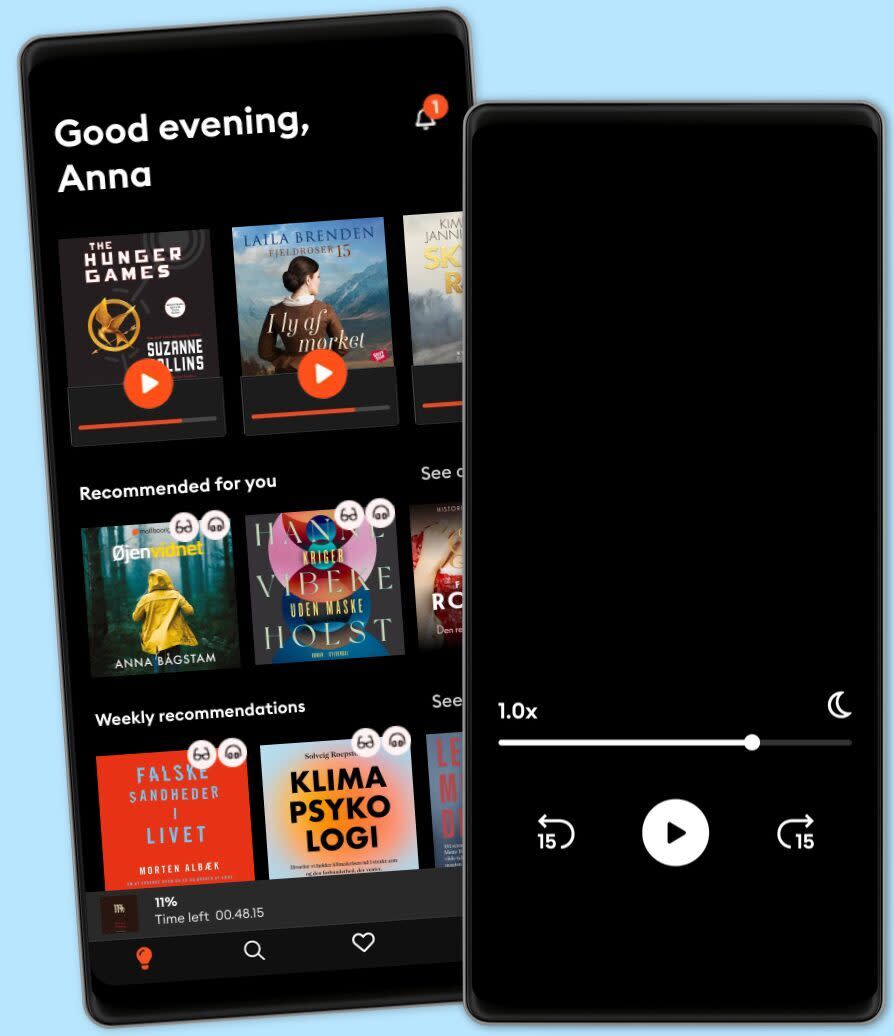
Lyt når som helst, hvor som helst
Nyd den ubegrænsede adgang til tusindvis af spændende e- og lydbøger - helt gratis
- Lyt og læs så meget du har lyst til
- Opdag et kæmpe bibliotek fyldt med fortællinger
- Eksklusive titler + Mofibo Originals
- Opsig når som helst
IT Security A Complete Guide - 2021 Edition
- Af
- Forlag
- Sprog
- Engelsk
- Format
- Kategori
Økonomi & Business
Are the computers of employees in unfiltered networks more often infected with malware?
Does management support security auditing by providing the right training for auditors?
Does your organization have an inventory of all third parties supporting the enterprise?
Is the code being integrated into the project fully vetted by IT management and approved?
What do you have within your organization relating to security of information and GDPR?
What has changed since the initial SOX compliance effort versus how things are done now?
What is the reputation and presence of the External Audit organization in its industry?
What threats are applicable in the environment in which the system will be operational?
Where do other organizations begin and move from reacting to anticipating cyber attacks?
Will the contract be performed at or near mission critical facility/capability locations?
This IT Security Guide is unlike books you're used to. If you're looking for a textbook, this might not be for you. This book and its included digital components is for you who understands the importance of asking great questions. This gives you the questions to uncover the IT Security challenges you're facing and generate better solutions to solve those problems.
Defining, designing, creating, and implementing a process to solve a challenge or meet an objective is the most valuable role… In EVERY group, company, organization and department.
Unless you're talking a one-time, single-use project, there should be a process. That process needs to be designed by someone with a complex enough perspective to ask the right questions. Someone capable of asking the right questions and step back and say, 'What are we really trying to accomplish here? And is there a different way to look at it?'
This Self-Assessment empowers people to do just that - whether their title is entrepreneur, manager, consultant, (Vice-)President, CxO etc... - they are the people who rule the future. They are the person who asks the right questions to make IT Security investments work better.
This IT Security All-Inclusive Self-Assessment enables You to be that person.
INCLUDES all the tools you need to an in-depth IT Security Self-Assessment. Featuring new and updated case-based questions, organized into seven core levels of IT Security maturity, this Self-Assessment will help you identify areas in which IT Security improvements can be made.
In using the questions you will be better able to:
Diagnose IT Security projects, initiatives, organizations, businesses and processes using accepted diagnostic standards and practices.
Implement evidence-based best practice strategies aligned with overall goals.
Integrate recent advances in IT Security and process design strategies into practice according to best practice guidelines.
Using the Self-Assessment tool gives you the IT Security Scorecard, enabling you to develop a clear picture of which IT Security areas need attention.
Your purchase includes access to the IT Security self-assessment digital components which gives you your dynamically prioritized projects-ready tool that enables you to define, show and lead your organization exactly with what's important.
© 2020 5STARCooks (E-bog): 9781867497912
Release date
E-bog: 11. december 2020
Andre kan også lide...
- Warrior Mindset - How to Cultivate a Warrior’s Mindset to Become Unstoppable in All Aspects of Your Life Empowered Living
- Artificial Intelligence: Data Analytics and Innovation for Beginners John Adamssen
- Cybersecurity: Learn Fast how to Become an InfoSec Pro 3 Books in 1 John Knowles
- Fit for a Queen Nicole Burnham
- Nox: An MM Paranormal Romance Stella Rainbow
- Certified Information Security Manager CISM Study Guide Mike Chapple, PhD, CISM
- The Yell-Free Parents' Guide to Disciplining an Explosive Child: Positive Parenting Strategies to Stop Yelling and Become a Peaceful Parent Rachel Barker
- Mindfulness For Dummies: 3rd Edition Shamash Alidina
- Python for Beginners: The dummies guide to learn Python Programming: A practical reference with exercises for newbie and advanced developers Mark Lioy
- My Favorite Sport: Baseball Nancy Streza
Vælg dit abonnement
Over 600.000 titler
Download og nyd titler offline
Eksklusive titler + Mofibo Originals
Børnevenligt miljø (Kids Mode)
Det er nemt at opsige når som helst
Premium
For dig som lytter og læser ofte.
1 konto
100 timer/måned
Eksklusivt indhold hver uge
Fri lytning til podcasts
Ingen binding
Unlimited
For dig som lytter og læser ubegrænset.
1 konto
Ubegrænset adgang
Eksklusivt indhold hver uge
Fri lytning til podcasts
Ingen binding
Family
For dig som ønsker at dele historier med familien.
2-6 konti
100 timer/måned pr. konto
Fri lytning til podcasts
Kun 39 kr. pr. ekstra konto
Ingen binding
2 konti
179 kr. /månedFlex
For dig som vil prøve Mofibo.
1 konto
20 timer/måned
Eksklusivt indhold hver uge
Fri lytning til podcasts
Gem ubrugt tid
Ingen binding
Dansk
Danmark