Who Are the Perfect Targets for Ransomware?
- Af
- Episode
- 63
- Published
- 23. jul. 2019
- Forlag
- 0 Anmeldelser
- 0
- Episode
- 63 of 336
- Længde
- 34M
- Sprog
- Engelsk
- Format
- Kategori
- Fakta
All images and links for this episode can be found on CISO Series (https://cisoseries.com/who-are-the-perfect-targets-for-ransomware/) If you've got lots of critical data, a massive insurance policy, and poor security infrastructure, you might be a perfect candidate to be hit with ransomware. This week and this week only, it's an extortion-free episode of CISO/Security Vendor Relationship Podcast. This episode is hosted by me, David Spark (@dspark), producer of CISO Series and founder of Spark Media Solutions and Mike Johnson. Our guest this week is Sean Walls (@sean_walls2000), vp, cybersecurity, Eurofins. Thanks to this week's podcast sponsor Core Security Assigning and managing entitlements rapidly to get employees the access they need is critical, but it can come at the cost of accuracy and security. Core Security’s identity governance and administration (IGA) solutions provide the intelligent, visual context needed to efficiently manage identity related security risks across any enterprise.
On this week's episode How CISOs are digesting the latest security news An article in the NYTimes points to a new trend in ransomware that is specifically attacking small governments with weak computer protections and strong insurance policies. Payments from $400-$600K. Lake City, Florida, population 12K paid $460K to extortionists. They got some of their information back but they have been set back years of what will require rescanning of paper documents. Mike, I know your standard philosophy is to not pay the ransom, but after a ransomware attack against the city of Atlanta, the mayor refused to pay $51,000 in extortion demands, and so far it's cost the city $7.2 million. Probably more. These payments by the small cities must be incentivizing more attacks. Does this information change the way you're willing to approach ransomware. What can a small city with zero cybersecurity staff do to create a program to reduce their risk to such a ransomware attack? Ask a CISO Bindu Sundaresan, AT&T Consulting Solutions, asks a very simple question, "How is each security initiative supporting the right business outcome?" Do you find yourself selling security into the business this way? If not, would you be more successful selling security to the business if you did do this? What's Worse?! We've got a split decision on what information we prefer after a breach. Listen up, it’s security awareness training time Jon Sanders, Elevate Security, said, "Security awareness involves A LOT of selling… there’s no cookie cutter approach in security awareness or sales!" Is the reason security training is so tough because so many security people are not born salespeople? I've interviewed many and there's a lot of "just listen to me attitude," which really doesn't work in sales.
Cloud Security Tip, sponsored by OpenVPN
We talk a lot about penetration testing here, given that it remains a staple of proactive IT security. But not everyone feels it’s all it’s cracked up to be. Or should that be, all it’s hacked up to be?” More than one cybersecurity organization points out there are a few flaws in the pen testing concept that make it worth a second look. Pen testing often consists of a small collection of attacks performed within a set time period against a small sample of situations. Some experts doubt the efficacy of testing against a limited field of known vulnerabilities, without knowing what other weaknesses exist in plain sight, or merely invisible to jaded eyes. More on CISO Series...
What do you think of this pitch? We have a pitch from Technium in which our CISOs question what exactly are they selling?
Who Are the Perfect Targets for Ransomware?
- Af
- Episode
- 63
- Published
- 23. jul. 2019
- Forlag
- 0 Anmeldelser
- 0
- Episode
- 63 of 336
- Længde
- 34M
- Sprog
- Engelsk
- Format
- Kategori
- Fakta
All images and links for this episode can be found on CISO Series (https://cisoseries.com/who-are-the-perfect-targets-for-ransomware/) If you've got lots of critical data, a massive insurance policy, and poor security infrastructure, you might be a perfect candidate to be hit with ransomware. This week and this week only, it's an extortion-free episode of CISO/Security Vendor Relationship Podcast. This episode is hosted by me, David Spark (@dspark), producer of CISO Series and founder of Spark Media Solutions and Mike Johnson. Our guest this week is Sean Walls (@sean_walls2000), vp, cybersecurity, Eurofins. Thanks to this week's podcast sponsor Core Security Assigning and managing entitlements rapidly to get employees the access they need is critical, but it can come at the cost of accuracy and security. Core Security’s identity governance and administration (IGA) solutions provide the intelligent, visual context needed to efficiently manage identity related security risks across any enterprise.
On this week's episode How CISOs are digesting the latest security news An article in the NYTimes points to a new trend in ransomware that is specifically attacking small governments with weak computer protections and strong insurance policies. Payments from $400-$600K. Lake City, Florida, population 12K paid $460K to extortionists. They got some of their information back but they have been set back years of what will require rescanning of paper documents. Mike, I know your standard philosophy is to not pay the ransom, but after a ransomware attack against the city of Atlanta, the mayor refused to pay $51,000 in extortion demands, and so far it's cost the city $7.2 million. Probably more. These payments by the small cities must be incentivizing more attacks. Does this information change the way you're willing to approach ransomware. What can a small city with zero cybersecurity staff do to create a program to reduce their risk to such a ransomware attack? Ask a CISO Bindu Sundaresan, AT&T Consulting Solutions, asks a very simple question, "How is each security initiative supporting the right business outcome?" Do you find yourself selling security into the business this way? If not, would you be more successful selling security to the business if you did do this? What's Worse?! We've got a split decision on what information we prefer after a breach. Listen up, it’s security awareness training time Jon Sanders, Elevate Security, said, "Security awareness involves A LOT of selling… there’s no cookie cutter approach in security awareness or sales!" Is the reason security training is so tough because so many security people are not born salespeople? I've interviewed many and there's a lot of "just listen to me attitude," which really doesn't work in sales.
Cloud Security Tip, sponsored by OpenVPN
We talk a lot about penetration testing here, given that it remains a staple of proactive IT security. But not everyone feels it’s all it’s cracked up to be. Or should that be, all it’s hacked up to be?” More than one cybersecurity organization points out there are a few flaws in the pen testing concept that make it worth a second look. Pen testing often consists of a small collection of attacks performed within a set time period against a small sample of situations. Some experts doubt the efficacy of testing against a limited field of known vulnerabilities, without knowing what other weaknesses exist in plain sight, or merely invisible to jaded eyes. More on CISO Series...
What do you think of this pitch? We have a pitch from Technium in which our CISOs question what exactly are they selling?
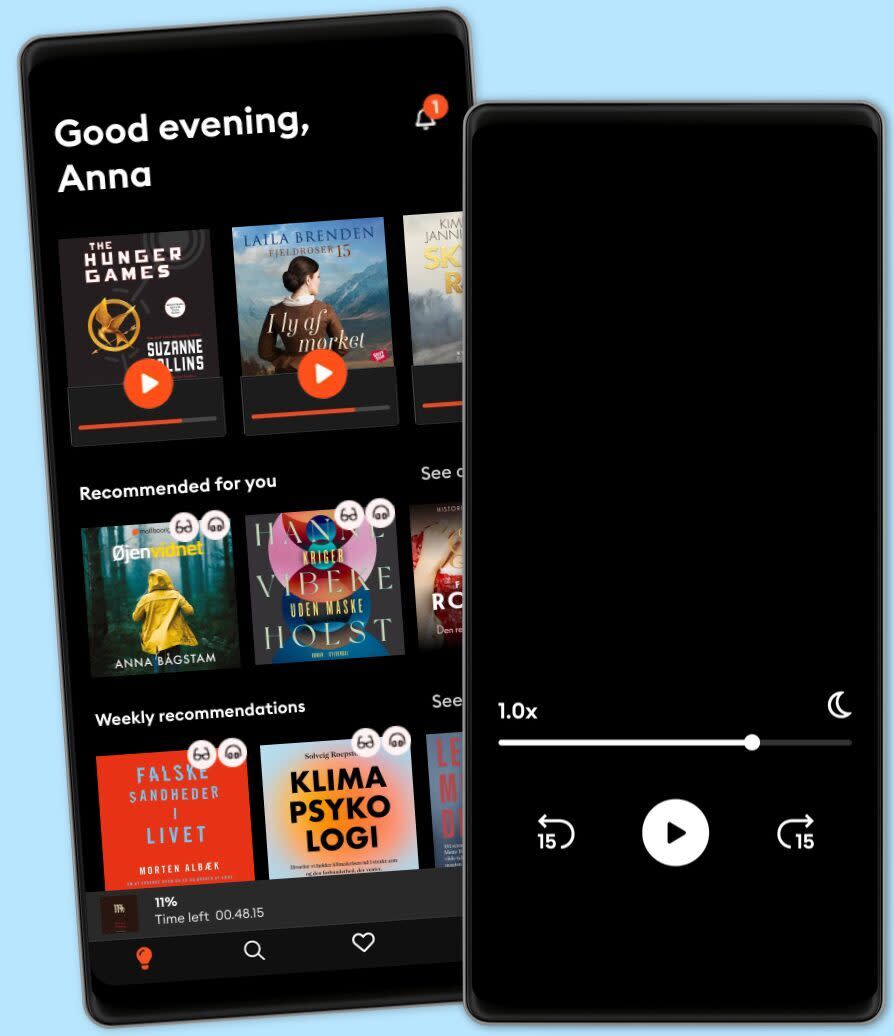
Lyt når som helst, hvor som helst
Nyd den ubegrænsede adgang til tusindvis af spændende e- og lydbøger - helt gratis
- Lyt og læs så meget du har lyst til
- Opdag et kæmpe bibliotek fyldt med fortællinger
- Eksklusive titler + Mofibo Originals
- Opsig når som helst
Other podcasts you might like ...
- This American LifeThis American Life
- The Book ReviewThe New York Times
- M’usa, con l’apostrofo. Le donne di PicassoLetizia Bravi
- FC PopCornFilm Companion
- News and ViewsThe Quint
- DiskoteksbrandenAntonio de la Cruz
- Dragon gateEdith Söderström
- En amerikansk epidemiPatrick Stanelius
- En värld i brand: Andra världskriget och sanningenAnton Vretander
- FamiljenFrida Anund
- This American LifeThis American Life
- The Book ReviewThe New York Times
- M’usa, con l’apostrofo. Le donne di PicassoLetizia Bravi
- FC PopCornFilm Companion
- News and ViewsThe Quint
- DiskoteksbrandenAntonio de la Cruz
- Dragon gateEdith Söderström
- En amerikansk epidemiPatrick Stanelius
- En värld i brand: Andra världskriget och sanningenAnton Vretander
- FamiljenFrida Anund
Dansk
Danmark