Vulnerability Management
- Af
- Episode
- 50
- Published
- 25. apr. 2019
- Forlag
- 0 Anmeldelser
- 0
- Episode
- 50 of 336
- Længde
- 21M
- Sprog
- Engelsk
- Format
- Kategori
- Fakta
This is a special episode of Defense in Depth being shared on this feed. Find the full post with links and images on the CISO Series site here (https://cisoseries.com/defense-in-depth-vulnerability-management/) So many breaches happen through ports of known vulnerabilities. What is the organizational vulnerability in vulnerability management? Check out this post and discussion and this one for the basis of our conversation on this week’s episode co-hosted by me, David Spark (@dspark), the creator of CISO Series and Allan Alford (@AllanAlfordinTX), CISO at Mitel. Our guest is Justin Berman (@justinmberman), CISO for Zenefits.
Vulcan’s vulnerability response automation platform allows enterprises to automate their TVM programs. Vulcan integrates to existing IT DevOps and security tools to fuse enterprise data with propriety intelligence which allows to accurately and subjectively priorities and remediate vulnerabilities - either using a patch workaround or compensating control.
On this episode of Defense in Depth, you'll learn: • As the CIS 20 concurs, vulnerability management is the first security measure you should take right after asset inventory. • Vulnerability management needs to be everyone's issue and managed by all departments. • Lots of discussion around vulnerability management being driven by culture which is a very hard concept to define. To get a "vulnerability management culture" look to a combination of awareness and risk management. • Vulnerabilities don't get patched and managed without someone taking on ownership. Without that, people are just talking and not doing. • Increased visibility across the life cycle of a vulnerability will allow all departments to see the associated risk. • Who are the risk owners? Once you can answer that questions you'll be able to assign accountability and responsibility.
Vulnerability Management
- Af
- Episode
- 50
- Published
- 25. apr. 2019
- Forlag
- 0 Anmeldelser
- 0
- Episode
- 50 of 336
- Længde
- 21M
- Sprog
- Engelsk
- Format
- Kategori
- Fakta
This is a special episode of Defense in Depth being shared on this feed. Find the full post with links and images on the CISO Series site here (https://cisoseries.com/defense-in-depth-vulnerability-management/) So many breaches happen through ports of known vulnerabilities. What is the organizational vulnerability in vulnerability management? Check out this post and discussion and this one for the basis of our conversation on this week’s episode co-hosted by me, David Spark (@dspark), the creator of CISO Series and Allan Alford (@AllanAlfordinTX), CISO at Mitel. Our guest is Justin Berman (@justinmberman), CISO for Zenefits.
Vulcan’s vulnerability response automation platform allows enterprises to automate their TVM programs. Vulcan integrates to existing IT DevOps and security tools to fuse enterprise data with propriety intelligence which allows to accurately and subjectively priorities and remediate vulnerabilities - either using a patch workaround or compensating control.
On this episode of Defense in Depth, you'll learn: • As the CIS 20 concurs, vulnerability management is the first security measure you should take right after asset inventory. • Vulnerability management needs to be everyone's issue and managed by all departments. • Lots of discussion around vulnerability management being driven by culture which is a very hard concept to define. To get a "vulnerability management culture" look to a combination of awareness and risk management. • Vulnerabilities don't get patched and managed without someone taking on ownership. Without that, people are just talking and not doing. • Increased visibility across the life cycle of a vulnerability will allow all departments to see the associated risk. • Who are the risk owners? Once you can answer that questions you'll be able to assign accountability and responsibility.
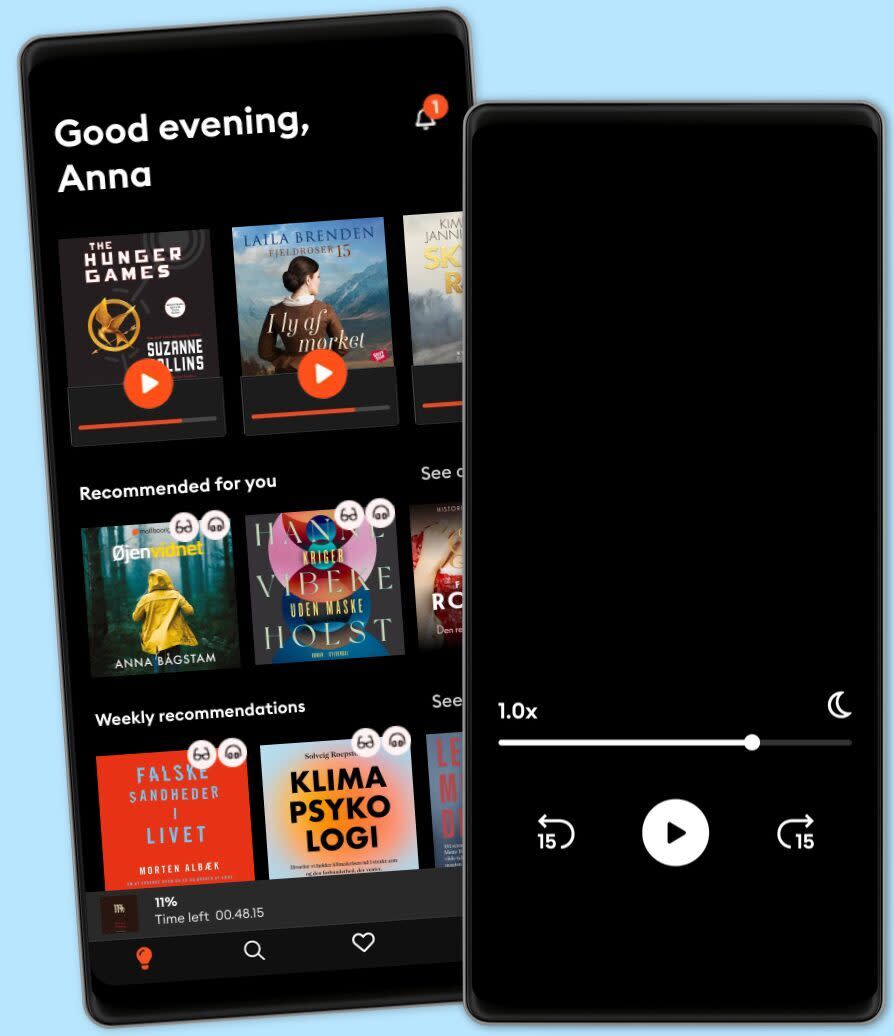
Lyt når som helst, hvor som helst
Nyd den ubegrænsede adgang til tusindvis af spændende e- og lydbøger - helt gratis
- Lyt og læs så meget du har lyst til
- Opdag et kæmpe bibliotek fyldt med fortællinger
- Eksklusive titler + Mofibo Originals
- Opsig når som helst
Other podcasts you might like ...
- This American LifeThis American Life
- The Book ReviewThe New York Times
- M’usa, con l’apostrofo. Le donne di PicassoLetizia Bravi
- FC PopCornFilm Companion
- News and ViewsThe Quint
- DiskoteksbrandenAntonio de la Cruz
- Dragon gateEdith Söderström
- En amerikansk epidemiPatrick Stanelius
- En värld i brand: Andra världskriget och sanningenAnton Vretander
- FamiljenFrida Anund
- This American LifeThis American Life
- The Book ReviewThe New York Times
- M’usa, con l’apostrofo. Le donne di PicassoLetizia Bravi
- FC PopCornFilm Companion
- News and ViewsThe Quint
- DiskoteksbrandenAntonio de la Cruz
- Dragon gateEdith Söderström
- En amerikansk epidemiPatrick Stanelius
- En värld i brand: Andra världskriget och sanningenAnton Vretander
- FamiljenFrida Anund
Dansk
Danmark