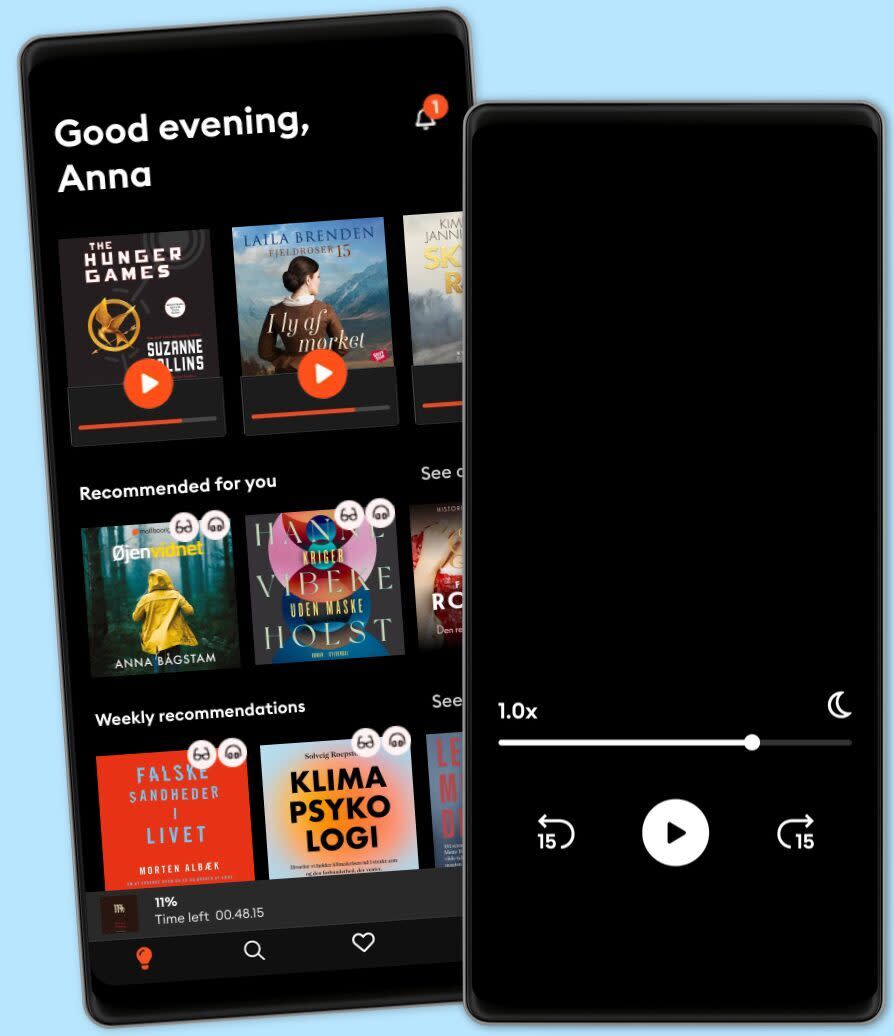
Lyt når som helst, hvor som helst
Nyd den ubegrænsede adgang til tusindvis af spændende e- og lydbøger - helt gratis
- Lyt og læs så meget du har lyst til
- Opdag et kæmpe bibliotek fyldt med fortællinger
- Eksklusive titler + Mofibo Originals
- Opsig når som helst
Security Management A Complete Guide - 2021 Edition
- Af
- Forlag
- Sprog
- Engelsk
- Format
- Kategori
Økonomi & Business
Can your organizations reuse existing resource management and configuration tools if any?
Does your organization use service contract or service level agreement for cloud services?
How well do your traditional network security tools/appliances work in cloud environments?
Is the cloud providers use of personal information clearly set out in its privacy policy?
What are your biggest operational, day to day headaches trying to protect cloud workloads?
What is an advantage of a cloud computing architecture over traditional IT architecture?
What limitations of liability, whether direct or indirect, is your organization granting?
What slas can be made so that the csp will aid your organization in performing forensics?
What specific services, facilities and system components were included in the validation?
Who has super admin access, either for a single SaaS application or multiple applications?
This Security Management Guide is unlike books you're used to. If you're looking for a textbook, this might not be for you. This book and its included digital components is for you who understands the importance of asking great questions. This gives you the questions to uncover the Security Management challenges you're facing and generate better solutions to solve those problems.
Defining, designing, creating, and implementing a process to solve a challenge or meet an objective is the most valuable role… In EVERY group, company, organization and department.
Unless you're talking a one-time, single-use project, there should be a process. That process needs to be designed by someone with a complex enough perspective to ask the right questions. Someone capable of asking the right questions and step back and say, 'What are we really trying to accomplish here? And is there a different way to look at it?'
This Self-Assessment empowers people to do just that - whether their title is entrepreneur, manager, consultant, (Vice-)President, CxO etc... - they are the people who rule the future. They are the person who asks the right questions to make Security Management investments work better.
This Security Management All-Inclusive Self-Assessment enables You to be that person.
INCLUDES all the tools you need to an in-depth Security Management Self-Assessment. Featuring new and updated case-based questions, organized into seven core levels of Security Management maturity, this Self-Assessment will help you identify areas in which Security Management improvements can be made.
In using the questions you will be better able to:
Diagnose Security Management projects, initiatives, organizations, businesses and processes using accepted diagnostic standards and practices.
Implement evidence-based best practice strategies aligned with overall goals.
Integrate recent advances in Security Management and process design strategies into practice according to best practice guidelines.
Using the Self-Assessment tool gives you the Security Management Scorecard, enabling you to develop a clear picture of which Security Management areas need attention.
Your purchase includes access to the Security Management self-assessment digital components which gives you your dynamically prioritized projects-ready tool that enables you to define, show and lead your organization exactly with what's important.
© 2020 5STARCooks (E-bog): 9781867497042
Release date
E-bog: 10. december 2020
Andre kan også lide...
- Facilities Energy Management A Complete Guide - 2021 Edition Gerardus Blokdyk
- Infrastructure Management A Complete Guide - 2021 Edition Gerardus Blokdyk
- Transportation Management System A Complete Guide - 2021 Edition Gerardus Blokdyk
- Financial Management: For Future Entrepreneur Suryaning Bawono
- Maximum Achievement: Strategies and Skills That Will Unlock Your Hidden Powers to Succeed Brian Tracy
- The Science of Motivation: Strategies and Techniques for Turning Dreams Into Destiny Brian Tracy
- Summary of Grit: The Power of Passion and Perseverance by Angela Duckworth Readtrepreneur Publishing
- Entrepreneurship for the Rest Us: How to Create Innovation and Opportunity Everywhere Paul B. Brown
- A damn good business: Make good money Ben Steenstra
- Guerrilla P.R. 2.0: Wage an Effective Publicity Campaign without Going Broke Michael Levine
Vælg dit abonnement
Over 600.000 titler
Download og nyd titler offline
Eksklusive titler + Mofibo Originals
Børnevenligt miljø (Kids Mode)
Det er nemt at opsige når som helst
Flex
For dig som vil prøve Mofibo.
1 konto
20 timer/måned
Eksklusivt indhold hver uge
Fri lytning til podcasts
Gem ubrugt tid
Ingen binding
Premium
For dig som lytter og læser ofte.
1 konto
100 timer/måned
Eksklusivt indhold hver uge
Fri lytning til podcasts
Ingen binding
Unlimited
For dig som lytter og læser ubegrænset.
1 konto
Ubegrænset adgang
Eksklusivt indhold hver uge
Fri lytning til podcasts
Ingen binding
Family
For dig som ønsker at dele historier med familien.
2-6 konti
100 timer/måned pr. konto
Fri lytning til podcasts
Kun 39 kr. pr. ekstra konto
Ingen binding
2 konti
179 kr. /månedDansk
Danmark