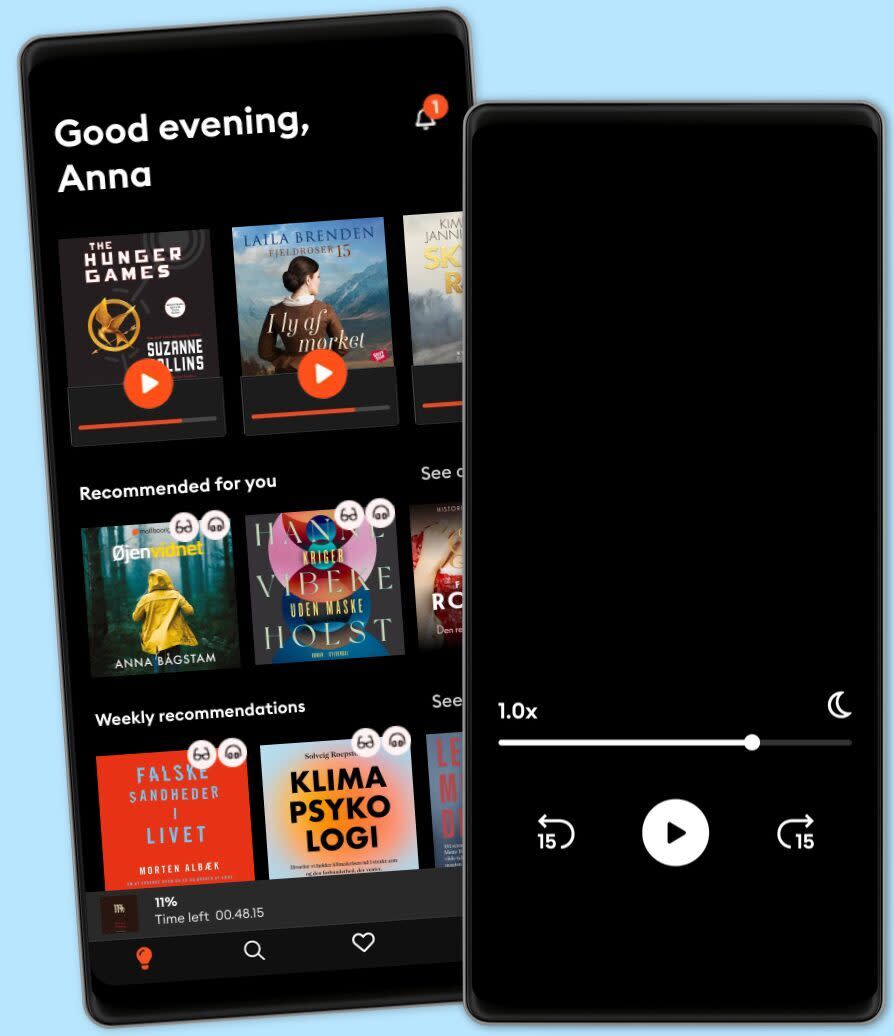
Lyt når som helst, hvor som helst
Nyd den ubegrænsede adgang til tusindvis af spændende e- og lydbøger - helt gratis
- Lyt og læs så meget du har lyst til
- Opdag et kæmpe bibliotek fyldt med fortællinger
- Eksklusive titler + Mofibo Originals
- Opsig når som helst
Information Security A Complete Guide - 2024 Edition
- Af
- Forlag
- Sprog
- Engelsk
- Format
- Kategori
Økonomi & Business
Are adequate confidentiality, integrity and availability in place for information security?
Are there existing communications and information security procedures and policies in place?
Do you face any challenges in collecting from/sharing information with other institutions?
Does management hold employees accountable for complying with information security policies?
How can findings be incorporated into the security investment strategies of organizations?
Is information security considered when hiring people for sensitive positions?
What are the key elements of your information security compliance program?
What is your organizations approach to implementing independent information security oversight?
What motivates the members of your organization to comply with information security policy?
Why should a small business be interested in, or concerned with information security?
This Information Security Guide breaks away from traditional books. If you're seeking a standard textbook, this may not be the right fit for you. This guide along with its accompanying digital resources is for you who understands the importance of asking profound questions. This equips you with the questions necessary to uncover the Information Security challenges you're confronting and devise superior solutions to address these issues.
Defining, designing, creating, and implementing a process to solve a challenge or achieve an objective is the most valuable role… Get Stuff Done in EVERY group, company, organization and department.
Unless you are dealing with a one-time, single-use project, there should be a process. That process needs to be designed by someone with a broad enough perspective to ask the right questions. Someone able to ask the right questions and step back and say, 'What are we really trying to accomplish here? And is there a different way to look at it?'
This Self-Assessment empowers people to do just that - whether their title is entrepreneur, manager, consultant, (Vice-)President, CxO etc... - they are the people who shape the future. They are the person who asks the right questions to make Information Security investments work better.
This Information Security All-Inclusive Self-Assessment enables You to be that person.
INCLUDES all the tools you need to an in-depth Information Security Self-Assessment. Featuring new and updated case-based questions, organized into seven core levels of Information Security maturity, this Self-Assessment will help you identify areas in which Information Security improvements can be made.
In using the questions you will be better able to:
Assess Information Security projects, initiatives, organizations, businesses and processes using established diagnostic standards and practices.
Implement evidence-based best practice strategies aligned with overall goals.
Integrate recent advances in Information Security and process design strategies into practice according to best practice guidelines.
Using the Self-Assessment tool gives you the Information Security Scorecard, enabling you to develop a clear picture of which Information Security areas need attention.
Your purchase includes access to the Information Security self-assessment digital components which gives you your dynamically prioritized project-ready tool. This tool enables you to define, show and lead your organization exactly with what's important.
© 2023 5STARCooks (E-bog): 9781038811486
Release date
E-bog: 3. november 2023
Andre kan også lide...
- Data Encryption A Complete Guide - 2021 Edition Gerardus Blokdyk
- Security Incidents A Complete Guide - 2024 Edition Gerardus Blokdyk
- IT Service Catalog A Complete Guide - 2021 Edition Gerardus Blokdyk
- Shopify Dropshipping Guide: How to build a $100K per Month Online Business in 2019. Combine Dropshipping, Affiliate Marketing, Email Marketing & Facebook Advertising into 1 Massive E-Commerce Business Marcus Rogers
- Information Science David G. Luenberger
- Information Security Handbook: Enhance your proficiency in information security program development Darren Death
- Infosec Rock Star: How to Accelerate Your Career Because Geek Will Only Get You So Far Ted Demopoulos
- Miss Fortescue's Protector in Paris Amanda McCabe
- Mastering Tableau 2023: Implement advanced business intelligence techniques, analytics, and machine learning models with Tableau Marleen Meier
- ServiceNow Cookbook: Acquire key capabilities for the ServiceNow platform Dustin Turner
Vælg dit abonnement
Over 600.000 titler
Download og nyd titler offline
Eksklusive titler + Mofibo Originals
Børnevenligt miljø (Kids Mode)
Det er nemt at opsige når som helst
Flex
For dig som vil prøve Mofibo.
1 konto
20 timer/måned
Eksklusivt indhold hver uge
Fri lytning til podcasts
Gem ubrugt tid
Ingen binding
Premium
For dig som lytter og læser ofte.
1 konto
100 timer/måned
Eksklusivt indhold hver uge
Fri lytning til podcasts
Ingen binding
Unlimited
For dig som lytter og læser ubegrænset.
1 konto
Ubegrænset adgang
Eksklusivt indhold hver uge
Fri lytning til podcasts
Ingen binding
Family
For dig som ønsker at dele historier med familien.
2-6 konti
100 timer/måned pr. konto
Fri lytning til podcasts
Kun 39 kr. pr. ekstra konto
Ingen binding
2 konti
179 kr. /månedDansk
Danmark