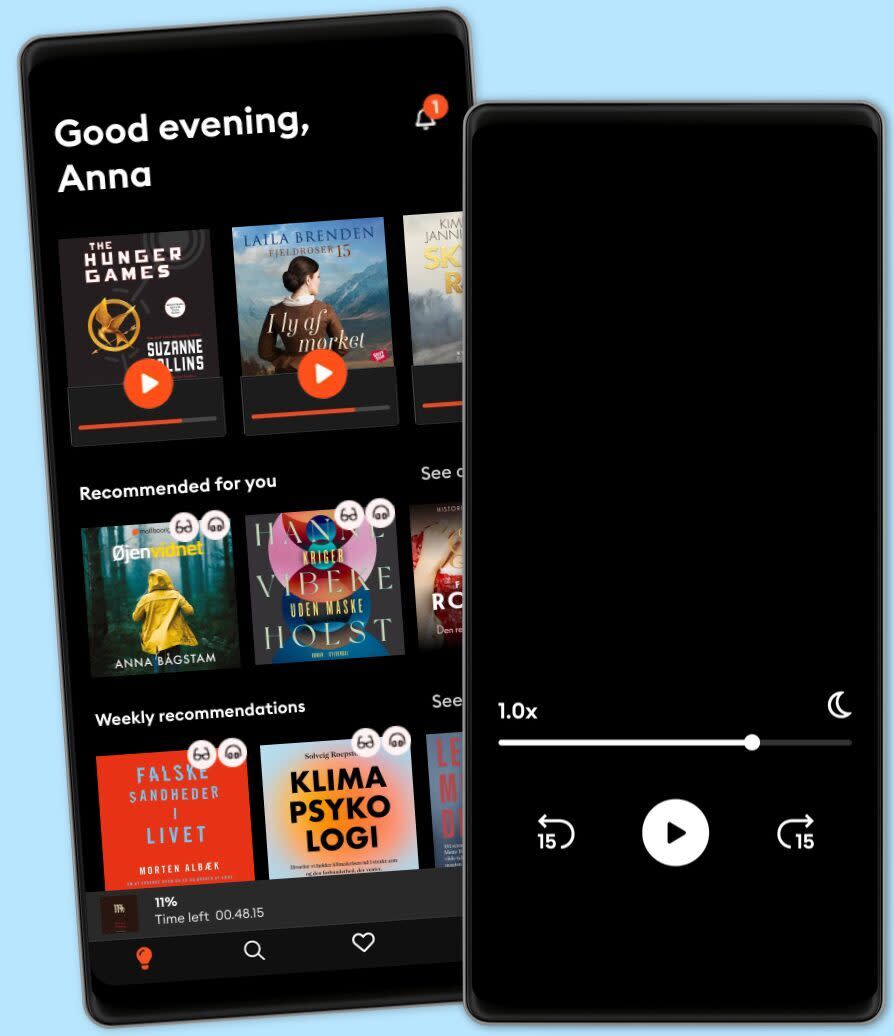
Lyt når som helst, hvor som helst
Nyd den ubegrænsede adgang til tusindvis af spændende e- og lydbøger - helt gratis
- Lyt og læs så meget du har lyst til
- Opdag et kæmpe bibliotek fyldt med fortællinger
- Eksklusive titler + Mofibo Originals
- Opsig når som helst
Debunking the Misused "Chased By Bear" Cybersecurity Metaphor
- Længde
- 36M
- Sprog
- Engelsk
- Format
- Kategori
Fakta
All links and images for this episode can be found on CISO Series (https://cisoseries.com/debunking-the-misused-chased-by-bear-cybersecurity-metaphor/) We don't want anyone to be caught by the bear on the latest episode of CISO/Security Vendor Relationship Podcast. This episode was recorded in person in San Francisco. It is hosted by me, David Spark (@dspark), producer of CISO Series and founder of Spark Media Solutions and Mike Johnson. Our sponsored guest this week is Elliot Lewis (@ElliotDLewis), CEO, Encryptics. Thanks to this week's podcast sponsor, Encryptics.
Now you can share data without ever losing control of it. Our advanced architecture makes data self-protecting, intelligent and self-aware – wherever it goes, no matter who has it. Our .SAFE patented multi-key technology enables data to evaluate its own safety conditions, including geo-sensing, recipient authentication, and policy changes from its owner. Contact Encryptics today and see for yourself.
On this week's episode Is this the best solution? On LinkedIn, Rich Malewicz of Wizer opened up a discussion of security is really just about making the lives difficult for attackers, or more difficult than another target. Rui Santos summed Rich's theory succinctly, "you don't have to be Fort Knox, just make it not worth the effort of hacking your organization." Let's dive into the specifics of this. Provide some examples of how you architect a security program that makes it too difficult or too costly for an attacker. Obviously, this would change given the asset you're trying to protect. The great CISO challenge Brad Green, Palo Alto Networks, asks, "What are the most important functions of the SOC (security operations center), and what are the most important activities that support them? What's Worse?! As always, both options stink, but one is worse. Please, Enough. No, More. Today's topic is data security. What have you heard enough about with data security, and what would you like to hear a lot more? Mike?
Communicating cyberthreats to the general public has always been a challenge for cybersecurity specialists, especially when it comes to eliciting cooperation in areas like cyberhygiene. Sometimes it helps to give people an awareness that the need for proactive security doesn’t exist only on screens, but everywhere. One fascinating example of this can be seen in the research of Dina Katabi of MIT, who has shown how WiFi signals can be monitored – not for their content, but as a form of radar that can see through walls, and which can accurately observe people physically moving around, or even detecting heartbeats and sleep patterns. Remote espionage opens up all kinds of opportunities for bad actors to build ergonomic profiles of anyone and then deploy AI and ML enabled analysis to influence and impersonate them. Showing people just how many different dimensions can be used in cybercrime may one day shift public perception of cybersecurity into the center spotlight where it belongs. More from our sponsor ExtraHop. There’s got to be a better way to handle this For years security professionals have talked about trying to secure the exponentially expanding surface area. One way to simplify, that we've all heard before, is driving security to the data level. Could we let networks run wild, within reason, and just have a data-security first approach? How is that different from zero trust, if at all? To what extent does this work/not work? We've all been having conversations about encryption for decades. It's not a new story. But it's still not universally used. There are billions of user accounts available in open text. After decades, why has the encryption story still not been getting through? What's holding back universal usage?
Release date
Lydbog: 21. januar 2020
Dansk
Danmark