Zero Trust Networks: Building Secure Systems in Untrusted Networks (2nd Edition)
- Længde
- 12T 5M
- Sprog
- Engelsk
- Format
- Kategori
Fakta
Perimeter defenses guarding your network aren't as secure as you might think. Hosts behind the firewall have no defenses of their own, so when a host in the "trusted" zone is breached, access to your data center is not far behind. This practical book introduces you to the zero trust model, a method that treats all hosts as if they're internet-facing, and considers the entire network to be compromised and hostile.
In this updated edition, the authors show you how zero trust lets you focus on building strong authentication, authorization, and encryption throughout, while providing compartmentalized access and better operational agility. You'll learn the architecture of a zero trust network, including how to build one using currently available technology.
You'll also explore fundamental concepts of a zero trust network, including trust engine, policy engine, and context aware agents; discover how this model embeds security within the system's operation, rather than layering it on top; use existing technology to establish trust among the actors in a network; migrate from a perimeter-based network to a zero trust network in production; examine case studies that provide insights into various organizations' zero trust journeys; and learn about the various zero trust architectures, standards, and frameworks.
© 2024 Ascent Audio (Lydbog): 9781663735584
Udgivelsesdato
Lydbog: 4. juni 2024
Andre kan også lide...
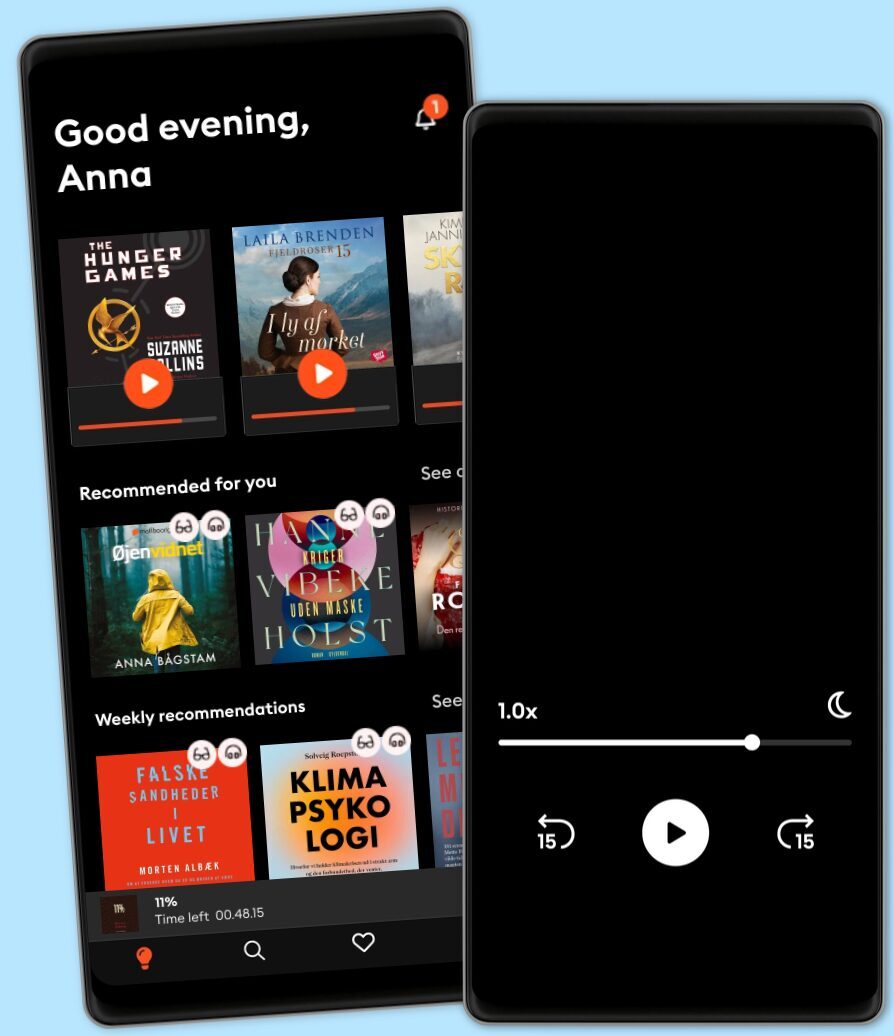
Vælg dit abonnement
Over 1 million titler
Download og nyd titler offline
Eksklusive titler + Mofibo Originals
Børnevenligt miljø (Kids Mode)
Det er nemt at opsige når som helst
Premium
For dig som lytter og læser ofte.
129 kr. /måned
Eksklusivt indhold hver uge
Fri lytning til podcasts
Ingen binding
Unlimited
For dig som lytter og læser ubegrænset.
159 kr. /måned
Eksklusivt indhold hver uge
Fri lytning til podcasts
Ingen binding
Family
For dig som ønsker at dele historier med familien.
Fra 179 kr. /måned
Fri lytning til podcasts
Kun 39 kr. pr. ekstra konto
Ingen binding
179 kr. /måned
Flex
For dig som vil prøve Mofibo.
89 kr. /måned
Gem op til 100 ubrugte timer
Eksklusivt indhold hver uge
Fri lytning til podcasts
Ingen binding
Har du en rabatkode?
Indtast koden her