Infrastructure Attack Strategies for Ethical Hacking
- Af
- Forlag
- Sprog
- Engelsk
- Format
- Kategori
Fakta
Defend Systems, Unveil Vulnerabilities, and Safeguard Infrastructure with Expert Strategies.
Book Description Embark on an immersive journey into the world of ethical hacking with "Infrastructure Attack Strategies for Ethical Hacking". From the initial stages of reconnaissance and enumeration to advanced techniques like attacking routers, databases, and Microsoft Windows systems, this handbook equips you with the skills needed for a comprehensive infrastructure compromise. ?? Encompassing both external and internal enumeration techniques, the book delves into attacking routers and services, establishing footholds, privilege escalation, lateral movement, and exploiting databases and Active Directory. You will gain proficiency in methodologies and tools for ethically compromising systems, navigating through networks, collecting intelligence, and providing effective remediation advice.
What you will learn - Master the intricacies of infrastructure attacks and ethical system compromise techniques. - Execute external and internal network reconnaissance to collect intelligence and pinpoint potential attack vectors. - Utilize routers, services, databases, and Active Directory to secure initial access, establish persistence, and enable lateral movement.
Table of Contents 1. Introduction to Infrastructure Attacks 2. Initial Reconnaissance and Enumeration 3. Attacking Routers 4. Looking for a Foothold 5. Getting Shells 6. Enumeration On Microsoft Windows 7. Enumeration on Linux 8. Internal Network Reconnaissance 9. Lateral Movement 10. Achieving First-level Pivoting 11. Attacking Databases 12. AD Reconnaissance and Enumeration 13. Path to Domain Admin 14. Playing with Hashes and Tickets Index
© 2024 Orange Education Pvt Ltd (E-bog): 9788196994747
Udgivelsesdato
E-bog: 4. marts 2024
Andre kan også lide...
- Summary, Analysis, and Review of Peter Schweizer's Profiles in Corruption: Abuse of Power by America's Progressive Elite Start Publishing Notes
- Summary, Analysis, and Review of Martha MacCallum's Unknown Valor: A Story of Family, Courage, and Sacrifice from Pearl Harbor to Iwo Jima Start Publishing Notes
- Modern API Design with gRPC Hitesh Pattanayak
- Mastering Large Language Models with Python Raj R
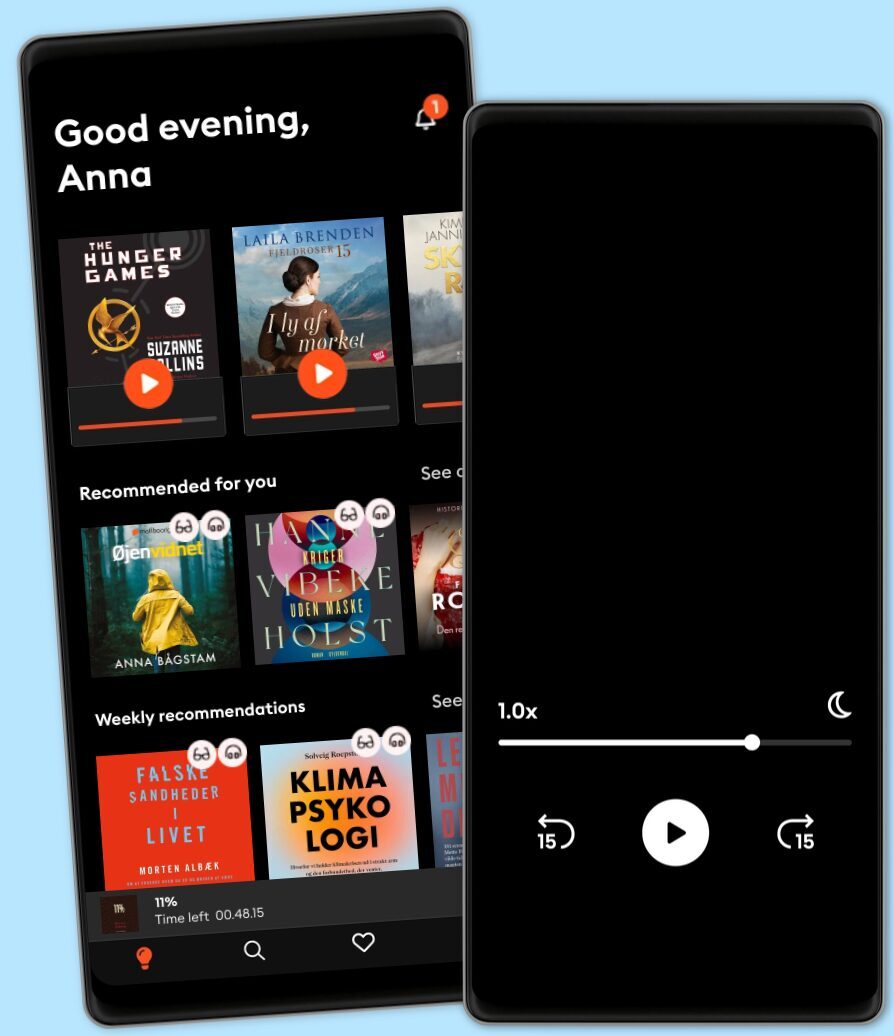
Vælg dit abonnement
Over 1 million titler
Download og nyd titler offline
Eksklusive titler + Mofibo Originals
Børnevenligt miljø (Kids Mode)
Det er nemt at opsige når som helst
Premium
For dig som lytter og læser ofte.
129 kr. /måned
Eksklusivt indhold hver uge
Fri lytning til podcasts
Ingen binding
Unlimited
For dig som lytter og læser ubegrænset.
159 kr. /måned
Eksklusivt indhold hver uge
Fri lytning til podcasts
Ingen binding
Family
For dig som ønsker at dele historier med familien.
Fra 179 kr. /måned
Fri lytning til podcasts
Kun 39 kr. pr. ekstra konto
Ingen binding
179 kr. /måned
Flex
For dig som vil prøve Mofibo.
89 kr. /måned
Gem op til 100 ubrugte timer
Eksklusivt indhold hver uge
Fri lytning til podcasts
Ingen binding
Har du en rabatkode?
Indtast koden her