Combatting Cyber Terrorism: A guide to understanding the cyber threat landscape and incident response planning
- Længde
- 6T 17M
- Sprog
- Engelsk
- Format
- Kategori
Fakta
In his second book with IT Governance Publishing, Richard Bingley's Combatting Cyber Terrorism – A guide to understanding the cyber threat landscape and incident response planning analyses the evolution of cyber terrorism and what organisations can do to mitigate this threat. This book discusses:
- Definitions of cyber terrorism; - Ideologies and idealisations that can lead to cyber terrorism; - How threat actors use computer systems to diversify, complicate and increase terrorist attack impacts; - The role of Big Tech and social media organisations such as X (formerly Twitter) and Instagram within the cyber threat landscape; and - How organisations can prepare for acts of cyber terrorism via security planning and incident response strategies such as ISO 31000, ISO 27001 and the NIST Cybersecurity Framework.Increasingly, cyber security practitioners are confronted with a stark phrase: cyber terrorism. For many, it conveys fear and hopelessness. What is this thing called 'cyber terrorism' and what can we begin to do about it? Malicious-minded ICT users, programmers and even programs (including much AI-powered software) have all been instrumental in recruiting, inspiring, training, executing and amplifying acts of terrorism. This has resulted in the loss of life and/or life-changing physical injuries that could never have occurred without support and facilitation from the cyber sphere. These types of attacks can be encapsulated by the phrase 'cyber terrorism'. This book recounts case studies to show the types of threats we face and provides a comprehensive coverage of risk management tactics and strategies to protect yourself against such nefarious threat actors. These include key mitigation and controls for information security or security and HR-related professionals.
© 2024 IT Governance Publishing Ltd (Lydbog): 9781787785229
Udgivelsesdato
Lydbog: 25. oktober 2024
Andre kan også lide...
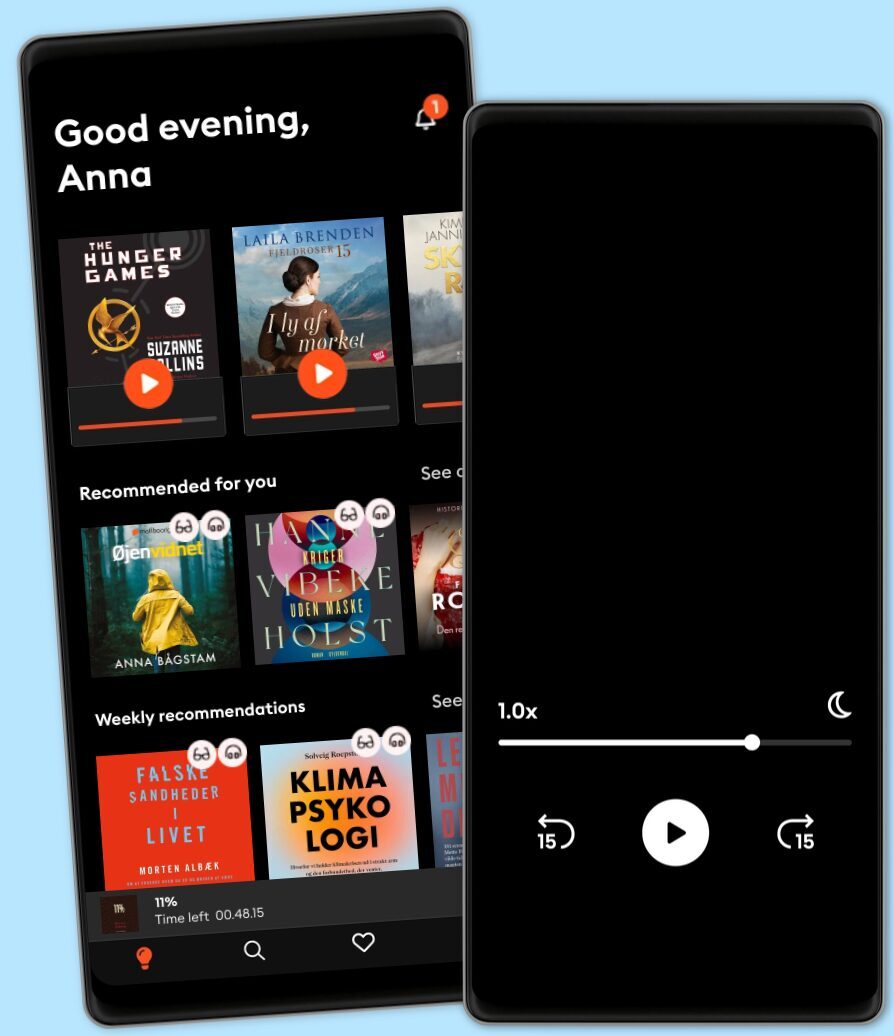
Vælg dit abonnement
Over 1 million titler
Download og nyd titler offline
Eksklusive titler + Mofibo Originals
Børnevenligt miljø (Kids Mode)
Det er nemt at opsige når som helst
Premium
For dig som lytter og læser ofte.
129 kr. /måned
Eksklusivt indhold hver uge
Fri lytning til podcasts
Ingen binding
Unlimited
For dig som lytter og læser ubegrænset.
159 kr. /måned
Eksklusivt indhold hver uge
Fri lytning til podcasts
Ingen binding
Family
For dig som ønsker at dele historier med familien.
Fra 179 kr. /måned
Fri lytning til podcasts
Kun 39 kr. pr. ekstra konto
Ingen binding
179 kr. /måned
Flex
For dig som vil prøve Mofibo.
89 kr. /måned
Gem op til 100 ubrugte timer
Eksklusivt indhold hver uge
Fri lytning til podcasts
Ingen binding
Har du en rabatkode?
Indtast koden her